Need for Change – Challenges for Companies in Using Distributed Ledger Technologies
Digital products and services are not only changing the everyday life of individuals or society. The new technologies on which they are based can also lead to changes in operational IT in a wide range of business areas, especially in service companies [1]. The distributed ledger technology, a new form of a distributed database, which ensures the integrity of all types of transactions without a central authority, is one such technology. Besides the question, in which areas it can be used, companies therefore also have to ask what internal impact can be expected when using this technology. In past DLT research projects of the BEI, it became apparent that companies must transform themselves holistically to implement DLT. They must not only build the technical know-how to handle the technology; due to the fact that a shared infrastructure is only possible if the business processes of all partners are aligned, they must work much more closely with partners and adapt all internal and external processes which involve DLT, coordinating them with all parties involved. In order to create synergies across companies, it is necessary for the companies involved to comply with business, process and technical standards. However, it has not yet been possible to identify the concrete transformation requirements that this will result in for individual business areas.
The challenges companies face when implementing distributed ledger technology and the impact it has on which business areas is the subject of this series of articles. The information presented here is the result of a research study conducted in cooperation with the Karlsruhe Institute of Technology (KIT) [2]. 15 experts shared their experiences from past DLT projects in the areas of finance and logistics. In this article, we first provide an overview of the 20 challenges we identified, before assigning them to the business functions they affect and addressing best practices in a second article. These contributions can serve as a basis for developing transformational mechanisms to change enterprise business functions and better understand DLT systems.
Distributed Ledger Technologies as an Alternative to Central IT Systems
Nowadays, companies rely heavily on centralized information systems (IS) to support their business processes, such as ERP systems for planning and controlling internal resources. These systems are usually managed and operated by a single entity, such as a company or its external IT provider [3].
However, cross-enterprise processes span entire business networks and require improved information flow to better manage collaboration between companies. However, centralized IS has limitations. For example, limited access makes it difficult for external parties to verify what is happening with their data. Extensive reliance on a single entity for management and operations can lead to opaque business practices and information asymmetries that weaken trust within the business network. An example is data within supply chains, which is not always visible or available to all or trustworthy due to the many interfaces between different actors who do not trust each other and use independent information systems. Inefficiencies arise on the one hand due to the time delay in the transmission of information, its multiple verification by different parties as well as possible errors in the transmission of information. On the other hand, the information asymmetry caused by non-interoperable systems makes it possible to manipulate, for example, freight documents or invoices [4].
Decentralized IS can compensate for these disadvantages by enabling companies to jointly manage, operate and use a system [5, 6]. They usually consist of a network of independent computers that allow distributed processing without a central authority. The best-known concepts for implementation are based on distributed ledger technologies (DLT) as well as their specific manifestations in the form of the blockchain, which serve as the basis for, e.g., many cryptocurrencies. DLT enables the operation of distributed databases (i.e., distributed ledgers) that are organized in a decentralized manner [7]. On these distributed ledgers services can be transacted, e.g., by recording transactions between actors (e.g., companies) or executing entire processes based on these transactions in an automated manner through formalized business logics (i.e., smart contracts). DLT systems can host multiple software applications that can be used by any member of the system.
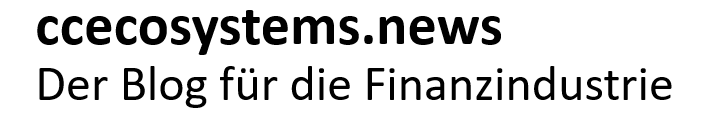
However, the introduction of DLT has implications for the enterprise that wishes to become part of such a system. FIG. 1 illustrates how the technical and organizational structures in a network change as a result of the shift from a centralized to a distributed information system: By introducing a distributed ledger, instead of having separate databases, companies now have a distributed, collaborative database that all companies can access at any time. A central coordinating instance is no longer required, and transparency in the network is increased. In order to be able to use this database, however, the companies must jointly agree on rules for how data can be added and stored or changed (business logic) and what the automated processes that the DLT can execute should look like. This increases the coordination requirements between the companies many times over [8]. These changes require a holistic transformation of business functions and the development of new competencies and capabilities. This may even lead to a structural reorganization, as it has been shown in the past that decreasing information asymmetries support the development of a flat organization instead of hierarchical structures [6]. While practitioners need to keep up with these developments, it is essential to know what organizational changes are occurring and what internal factors are undergoing change.
Challenges in the Use of Distributed Ledger Technologies
To identify the challenges in the use of DTL, expert interviews were conducted with practitioners who had an average experience with DLT projects of 4.9 years. The identified challenges were then grouped and aggregated into overarching areas. Next, these areas were related to three key elements that frame enterprise technology adoption [9]: The way in which a company uses a new technology is determined by the technological framework conditions (e.g. technology access), the organizational context (e.g. corporate structure) and the environmental conditions (e.g. regulation). The next sections present the overarching areas and describe the challenges most frequently mentioned by the experts for each of the three dimensions.
Technological Challenges
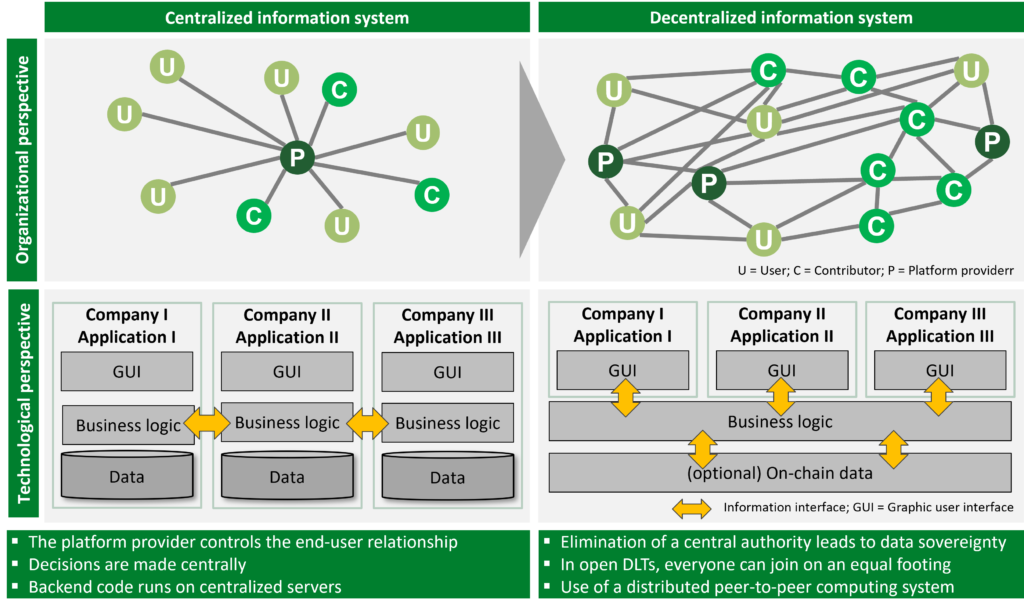
The technological context takes into account all the challenges that arise when implementing DLT in an organization and that can be attributed to characteristics of DLT itself, i.e., potential functionalities or technical limitations [2] As shown in Table 1, three domains with a total of nine challenges have been identified in this dimension: IT system engineering, IT administration, and user-centered application design.
IT Administration: The area IT administration refers to the various challenges associated with the tasks and responsibilities in managing software systems, source code maintenance and system administration.
Cryptographic key management: This challenge refers to the effort associated with the creation, custody and use of cryptographic keys (private keys) for interaction with the underlying DLT (e.g. signing transactions). The role of the key owner is responsible for safekeeping (non-custodial) and the keys often cannot be recovered if lost. Since, in contrast to conventional passwords, it is not possible to simply generate a new private key for an existing account, managing private keys requires new measures and additional security effort to increase their protection, e.g., in the event of cyberattacks: “[…] someone in the organization must have the keys, or there must be a procedure, a two-person rule, to ensure that the correct transactions are executed or not. The keys [must be] shared or recoverable. It’s not that simple.” (Product manager). As one innovation manager explained, “[…] custody is currently outsourced to specialist providers”. Organizations interacting directly with DLT need to implement new processes from scratch to manage keys on behalf of their employees or customers.
User-centered application design: This area covers all challenges associated with making DLT-based systems user-friendly.
Usability: challenges refer to the difficulties end users face when using services provided by DLT systems, such as. decentralized finance applications (DeFi). While conventional apps typically require a username and password for authentication, decentralized apps (DApps) rely on unwieldy digital signatures generated from a cryptographic key (i.e., a private key). “[…] there is a risk that employees are overwhelmed, because I often see that DApps are terribly complicated in terms of user experience. The key unique selling point has always been that it’s handled through blockchain, and that’s not an argument for using such technology in a business ” (Chief Executive Officer). You can find an example of such a user experience involving the use of the crypto wallet MetaMask at this link. New design principles are needed to meet the requirements for using DLT systems for non-technology-savvy users (e.g., signing transactions).
We’ll look at organizational and environmental challenges next week in the second part of this post. The update will be published next Tuesday. If you want to be informed directly, you can register on the right side of this page or follow us on LinkedIn.